PHI: Path-Hidden Lightweight Anonymity Protocol at Network Layer
Authors: Chen Chen (Carnegie Mellon University / ETH Zurich), Adrian Perrig (ETH Zurich)
Volume: 2017
Issue: 1
Pages: 100–117
DOI: https://doi.org/10.1515/popets-2017-0007
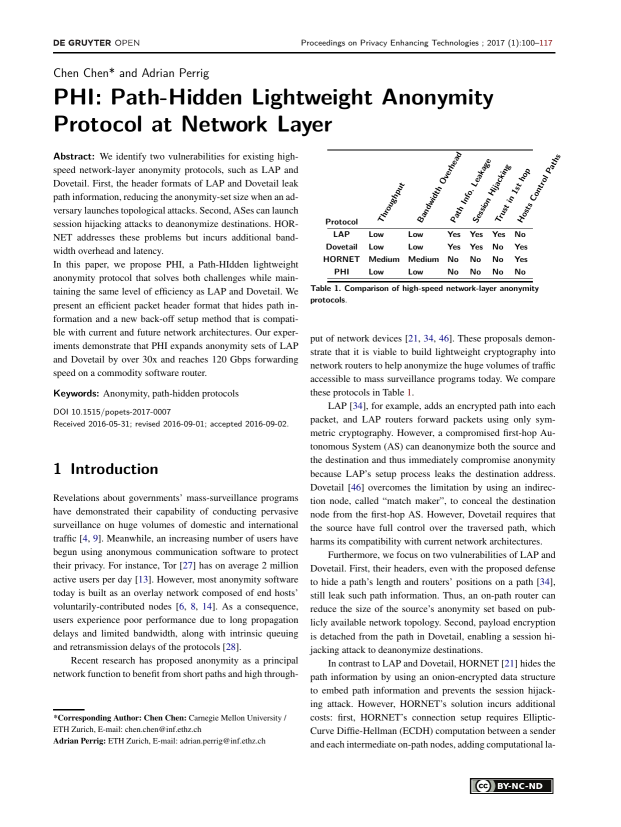
Abstract: We identify two vulnerabilities for existing highspeed network-layer anonymity protocols, such as LAP and Dovetail. First, the header formats of LAP and Dovetail leak path information, reducing the anonymity-set size when an adversary launches topological attacks. Second, ASes can launch session hijacking attacks to deanonymize destinations. HORNET addresses these problems but incurs additional bandwidth overhead and latency. In this paper, we propose PHI, a Path-HIdden lightweight anonymity protocol that solves both challenges while maintaining the same level of efficiency as LAP and Dovetail. We present an efficient packet header format that hides path information and a new back-off setup method that is compatible with current and future network architectures. Our experiments demonstrate that PHI expands anonymity sets of LAP and Dovetail by over 30x and reaches 120 Gbps forwarding speed on a commodity software router.
Keywords: Anonymity, path-hidden protocols
Copyright in PoPETs articles are held by their authors. This article is published under a Creative Commons Attribution-NonCommercial-NoDerivs 3.0 license.