Keeping the Smart Home Private with Smart(er) IoT Traffic Shaping Sleeping habits – Sense Sleep Monitor
Authors: Noah Apthorpe (Princeton University, Department of Computer Science), Danny Yuxing Huang (Princeton University, Department of Computer Science), Dillon Reisman (Princeton University, Department of Computer Science), Arvind Narayanan (Princeton University, Department of Computer Science), Nick Feamster (Princeton University, Department of Computer Science)
Volume: 2019
Issue: 3
Pages: 128–148
DOI: https://doi.org/10.2478/popets-2019-0040
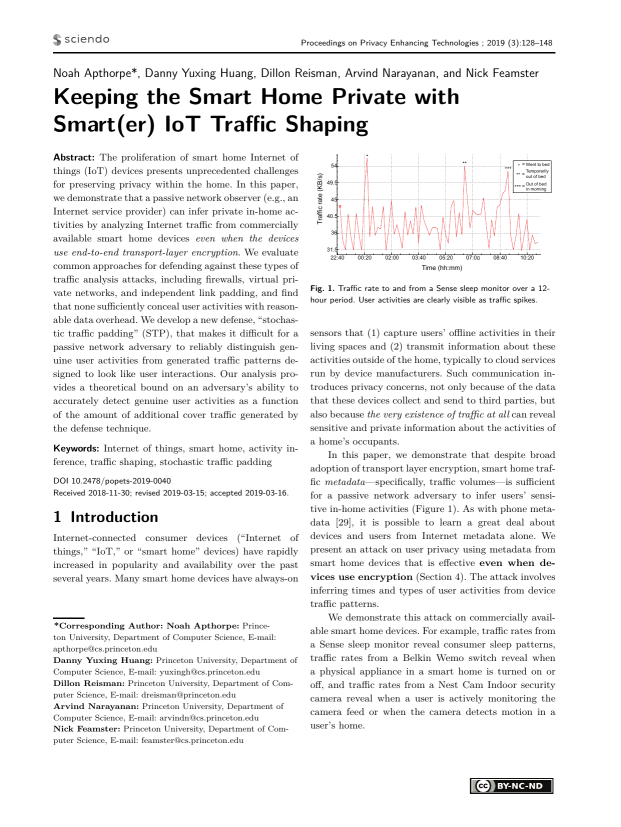
Abstract: The proliferation of smart home Internet of things (IoT) devices presents unprecedented challenges for preserving privacy within the home. In this paper, we demonstrate that a passive network observer (e.g., an Internet service provider) can infer private in-home activities by analyzing Internet traffic from commercially available smart home devices even when the devices use end-to-end transport-layer encryption. We evaluate common approaches for defending against these types of traffic analysis attacks, including firewalls, virtual private networks, and independent link padding, and find that none sufficiently conceal user activities with reasonable data overhead. We develop a new defense, “stochastic traffic padding” (STP), that makes it difficult for a passive network adversary to reliably distinguish genuine user activities from generated traffic patterns designed to look like user interactions. Our analysis provides a theoretical bound on an adversary’s ability to accurately detect genuine user activities as a function of the amount of additional cover traffic generated by the defense technique.
Keywords: Internet of things, smart home, activity inference, traffic shaping, stochastic traffic padding
Copyright in PoPETs articles are held by their authors. This article is published under a Creative Commons Attribution-NonCommercial-NoDerivs 3.0 license.